Security groups
Security groups control network traffic to or from an AWS EC2 instance according to a set of inbound and outbound rules. Security groups evaluate all the rules in them before allowing network traffic. Security groups, by default, do not allow any inbound network traffic but allow all outbound network traffic. When you create a VPC, AWS automatically creates a default security group for it. Similar to network ACLs, the IT auditor needs to review the rules in the security group to ensure inbound and outbound network traffic is authorized by the organization. In particular, pay close attention to the source, destination, protocol, and port ranges for both inbound and outbound rules.
While you could implement security groups independent of network ACLs, it is recommended to implement both as security groups and network ACLs are two layers that complement each other as part of defense in depth. Network ACLs are the first line of defense, whereas security groups are the second line of defense for inbound network traffic. For outbound network traffic, security groups are the first line of defense, while network ACLs are the second layer of defense.
To review security groups in AWS, click on Security Groups under the Resources by Region AWS interface, as shown in Figure 4.25:
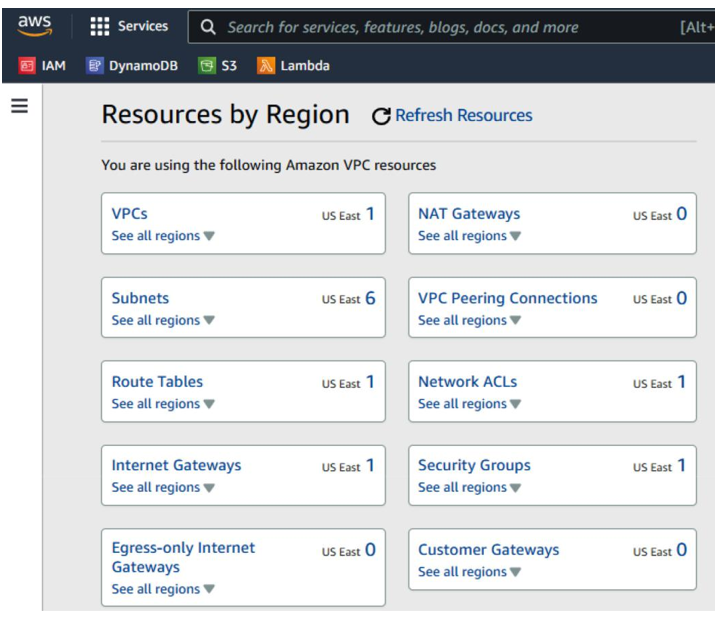
Figure 4.25 – AWS Resources by Region
A list of security groups will be displayed, as shown in Figure 4.26:
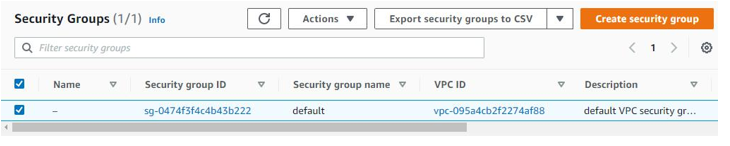
Figure 4.26 – AWS – Security Groups
Details of the Security Group are shown in Figure 4.27:
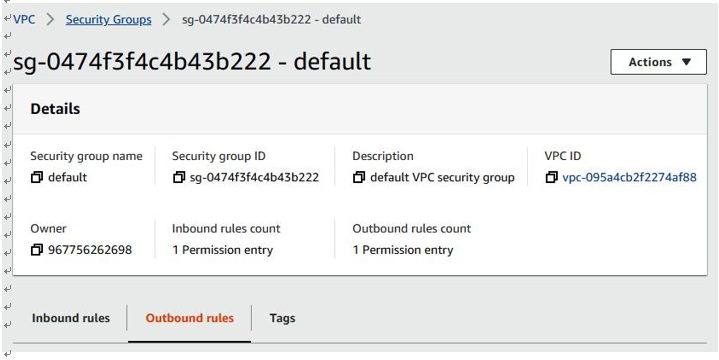
Figure 4.27 – AWS Security Group details
Review Inbound rules, as shown in Figure 4.28:
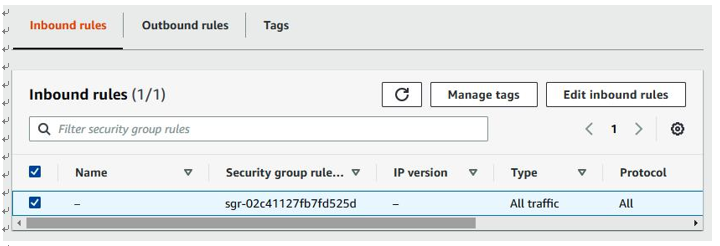
Figure 4.28 – AWS Inbound rules
Review Outbound rules, as shown in Figure 4.29:
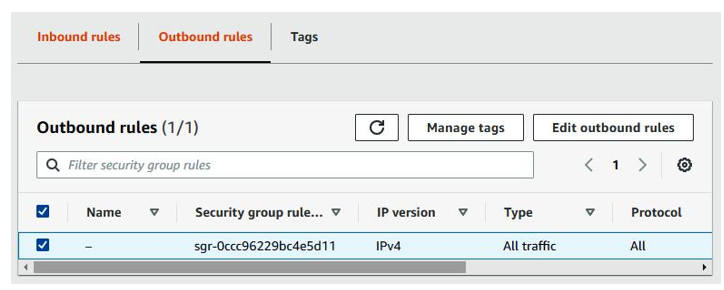
Figure 4.29 – AWS Outbound rules
Now that we’ve looked at how to secure network controls for an AWS VPC, let’s look at how to implement network security controls in an Azure VNet.


