Network ACLs
Network ACLs manage network traffic at the subnetwork level. Network ACLs keep unwanted network traffic out of the subnets. Subnets or subnetworks are smaller separate parts of the overall VPC. Network ACLs allow or disallow network traffic based on the configured policy. NACLs are stateless, so they must be configured inbound or outbound. NACLs rules are processed in order, so order matters.
Network ACLs control network traffic to or from a subnet according to a set of inbound and outbound rules. This means they represent network-level security. For example, an inbound rule might deny incoming network traffic from a range of IP addresses originating from a hostile country, while an outbound rule might allow all network traffic to leave the subnet.
All AWS accounts come with a default VPC. A default VPC comes with a public subnet. As an IT auditor, it is important to ensure no sensitive company data is placed in a public subnet. In addition, the default VPC has a network ACL, which allows all inbound and outbound network traffic. The IT auditor needs to review the rules in the default VPC network ACL to ensure inbound and outbound network traffic is authorized by the organization. In particular, pay close attention to the source, destination, protocol, and port ranges for both inbound and outbound rules. In addition, AWS rules are evaluated in numerical order, starting with the lowest-numbered rule getting processed first. Therefore, it is important to examine if the rules have been placed in the proper order.
To review network ACLs in AWS, click on Network ACLs under the Resources by Region AWS interface, as shown in Figure 4.21:
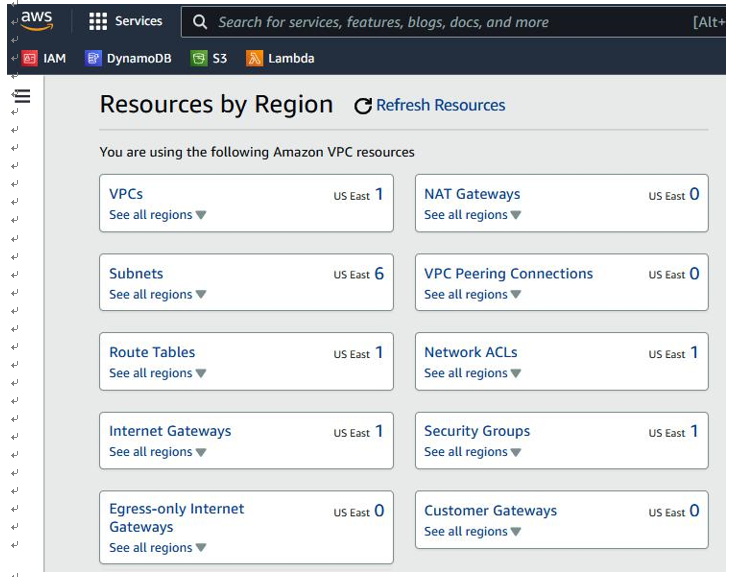
Figure 4.21 – AWS Resources by Region
A list of network ACLs will be displayed, as shown in Figure 4.22:
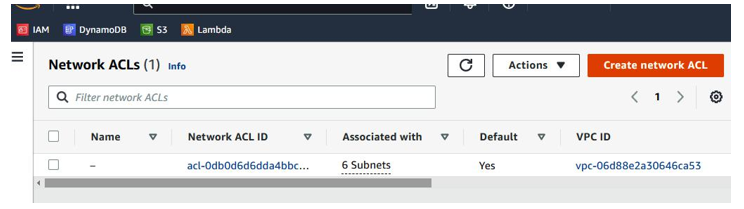
Figure 4.22 – AWS – Network ACLs
Review Inbound rules, as shown in Figure 4.23:
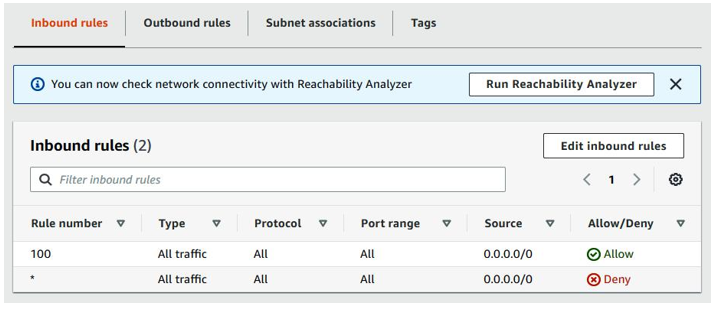
Figure 4.23 – AWS Inbound rules
Review Outbound rules, as shown in Figure 4.24:
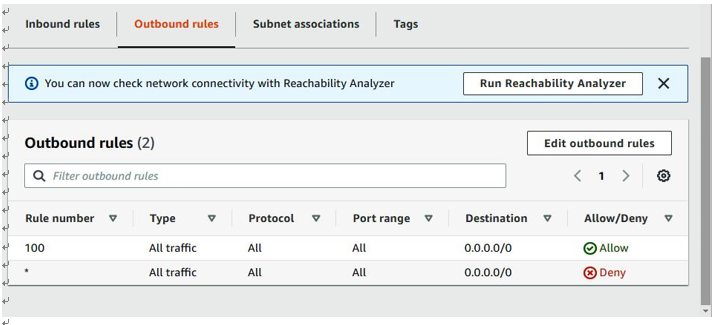
Figure 4.24 – AWS Outbound rules
In the example shown in Figure 4.23, rule 100 for inbound rules with source 0.0.0.0/0 means the VPC allows inbound access from all IP addresses for all port ranges and protocols. In the example in Figure 4.24, rule 100 for outbound rules with destination 0.0.0.0/0 means the VPC allows outbound access from all IP addresses for all port ranges and protocols. In this scenario, the IT auditor should question the organization as to the business case of maintaining a VPC with insecure rules.
Security groups are another network control for managing network traffic. We’ll look at them next.


